QR codes were first invented to be used for inventory tracking. As they’re extremely easy to use, their usage became widespread across industries like advertising, product authentication, and more. However, with the growing popularity comes the rise of malicious intent of scammers, putting QR code security at risk. Brands need to implement new ways to combat this increasing danger to safeguard their reputation and customers.
The unique problem with QR codes is the lack of any method to verify their authenticity before scanning them. With the advanced technology and tools available, scammers can easily replace the genuine QR code by sticking a fake one over it. Or worse, they can create an entire counterfeit packaging with a fake QR code to appear legitimate.
This puts consumers at risk of becoming a victim of a phishing attack or a scam. In fact, 71% of people can’t tell a fake QR code from a real one.
These scams have become so prominent that the FBI issued a warning in 2021 regarding QR codes’ security, spreading awareness about malicious QR codes.
Brands using QR codes have an inherent responsibility of securing their QR codes so that their customers can prevent such cybersecurity attacks. If you’re using QR codes for product verification, secured QR codes will help prevent product counterfeiting too. Fake QR codes will make a dent in your brand reputation, more so if your products are counterfeited.
What Are QR Codes?
QR codes are two-dimensional barcode-like structures that store information in a matrix of black and white squares. A user can access the stored data by a quick scan via a mobile phone camera app or a dedicated scanning device. They are used in multiple ways, from traceability of products and accessing dedicated websites to redeeming exclusive offers.
These codes truly bridge the gap between the physical and digital realms, improving customer experiences.
While QR codes are useful in product traceability, they shouldn’t be mistakenly assumed as an anti-counterfeiting solution – QR codes can’t double up as an anti-counterfeiting solution.
The reason: Traceability merely helps in providing product information, and can’t serve as a security feature for product authenticity. If a product itself is fake, the traceability information in QR codes holds no importance. This is why QR codes should always be complemented with added security features.
The History of QR Codes
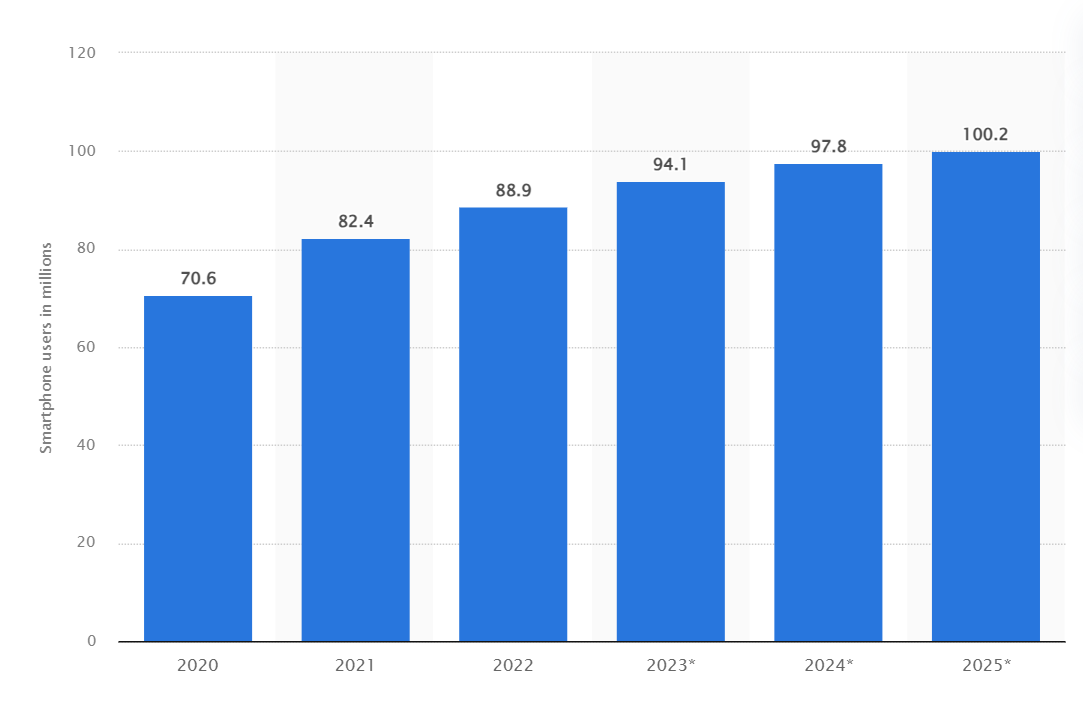
QR codes have become extremely popular in recent years, popping up on everything from business cards to gravestones. Since the pandemic, its usage has increased further due to its contact-less nature. In 2022, 89 million people scanned a QR code in the US alone, which is 26% more than in 2020. This number is expected to exceed 100 million by 2025.
Given its popularity, it’s hard to believe that just 30 years ago, they didn’t even exist.
QR codes were first developed in Japan in 1994 at a company called Denso, which produced automotive parts. One of the company’s employees, Hara Masahiro, noticed that the standard line barcodes used to track their products were inefficient and time-consuming to use. The barcodes could only store limited amounts of information, so in some cases, product boxes had up to ten barcodes on them, and they had to be scanned multiple times during the shipping process.
Masahiro saw the need for a new kind of technology that could store more information. He had a flash of insight when playing a grid-based strategy game that gave him the idea to create a two-dimensional pattern of black and white square dots. His team developed what ultimately became known as quick response codes or QR codes.
They became part of the mainstream use when cell phones with cameras began hitting the market, allowing the average user to scan and access information using their digital device quickly.
Can QR Code Be a Security Risk?
QR codes are not inherently secure or unsecured. They serve as a convenient way to transfer data, but like any technology, their security relies on how they are implemented and used. For example, the content they link to can pose a risk if it’s hacked or counterfeited.
Before QR codes, cybercriminals usually used email and SMS for a phishing and malware attack. However, today, consumers can tell a scam email as there are many indications of the scam. For example, the email might read with common spelling errors or the linked URL might seem fishy. 67% of people can identify between a malicious link and a genuine one.
There are no such signs when it comes to QR codes. As the URL links redirected from the codes can’t be seen before the actual scan, it puts consumers at risk of scanning to a malicious site.
When a fake QR code is used on products, consumers can’t verify the authenticity of the products. Counterfeiters take advantage of this ambiguity by swapping the legitimate products with a fake product, supported with fake QR codes.
Potential QR Code Security Risks
While QR codes provide a great many benefits, the truth is that they are not as effective, especially at product authentication. When a QR code is used for product authentication, it can be faked, helping counterfeiters fool consumers.
There are several other instances when QR codes put consumers in danger:
Erased or Removed from Products
If your QR code is being used in track-and-trace of products, they can be easily removed. Just like serial numbers can be filed off electronics and other high-value products and then sold in the counterfeit market, so can QR codes, erasing the supply chain information.
Copied Codes
QR codes are simple to recreate and reproduce. That’s part of why they are so popular in inventory management—they’re easy to generate and affix to products. Unfortunately, it’s also what makes them vulnerable to counterfeiting. Bad actors can simply copy a manufacturer’s QR code and pass it off as genuine.
Fake codes
Many consumers don’t even bother to scan a QR code on a product. They merely see it included in the product and assume the product’s legitimacy. Counterfeiters can use this to their advantage by creating fake QR codes that contain inaccurate information or no information whatsoever.
This type of QR code is also used in other places apart from product authentication. For example, in a social place, a fake QR code leading to a malicious website can put the public at risk. This type of phishing scam is also called QRishing. QR codes can also be used to steal personal contact and identity details of a user.
The same is true for products. Counterfeiters can implement such attacks while also creating fake products.
While QR codes have so many weaknesses, they still create a false sense of security. Consumers may see a QR code on a product and just assume that its presence means the product is authentic, not realizing that a QR code on its own is not a security feature.
Importance of Secured QR Codes
By prioritizing QR code security, company owners show their commitment to customer safety and data protection. This helps customers to feel confident in engaging with QR codes associated with the brand, increasing customer trust and loyalty. Different use cases of secured QR codes are:
Supply Chain and Product Authentication
Without tight control of the supply chain, counterfeit products can find their way into the hands of the consumer. To prevent the damage this can do to both the consumer and the company’s reputation, stakeholders at every point in the supply chain must be held responsible for the authenticity of the products they are handling.
Even though they recognize the seriousness of counterfeiting, many companies are at a loss as to how to hold stakeholders in the supply chain responsible for counterfeit products. It’s no longer enough to rely on one form of security to deter counterfeiters.
The counterfeit market has become so sophisticated that counterfeiters can make imitation products that are virtually indistinguishable by consumers and even by industry experts, as well. This is why advanced and invisible security technology like secured QR codes is one of the best available solutions.
Payment
Payment breaches resulting from fake QR code lead to financial losses for both brand owners and customers. Securing your QR codes minimizes the risk of fraudulent payment activities, protecting your financial stability and customer investments.
Current Solutions to Avoid QR Code Security Threats
There are limited solutions with varying effectiveness in the market when it comes to your QR code’s safety.
- Custom branding: You can make your QR codes appear unique by incorporating your branding in the QR codes. You can include your brand logo, color, and styling so that users can identify genuine QR codes. However, this isn’t hard to replicate by the counterfeiters.
- Combining hologram with QR code: Hologram is often added as an extra security feature, but again, it’s not foolproof. Holograms are visible to the nake eye and can be easily copied. While the scammers and counterfeiters might not be able to generate the refined color difference of the legitimate hologram, it doesn’t impact the perception of consumers. An everyday user can’t tell the difference between the refined and sophisticated genuine hologram and a counterfeited sticker of hologram.
- Password protection: You can protect your QR codes’ sensitive information with a password. However, this only works if you’re sharing the QR codes with a close group of people, which is not the case when it comes to product distribution or other public QR codes.
Multi-layered Advanced Solution to Secure QR Codes
To transform QR codes into reliable anti-counterfeiting tools, extra features need to be built into them to make them less easy to copy and fake.
For example, AlpVision has developed a “secured QR code,” which incorporates micro holes in the QR code at the printing stage. They are included randomly and users can ddetect them by a dedicated mobile phone app. The design of the QR code is unchanged, so this added security feature can’t be seen by the naked eye. It’s only picked up when users scan the QR code via a mobile phone camera app.
Counterfeiters who try to copy the secured QR code won’t be able to replicate these micro holes, which are just 20 to 40 microns in size.
Secure Your QR Codes with AlpVision
QR code security isn’t just about protecting your brand – it’s about safeguarding the trust and loyalty of your customers. No matter how you use these codes, you need additional layers of security. With a secured QR code, you continue to establish a strong brand presence and customer satisfaction.
At AlpVision, our mission is to develop the most cutting-edge anti-counterfeiting solutions that are simple to use but impossible to copy or fake. Find out more about how AlpVision’s anti-counterfeiting solutions can protect your products here :
Learn More